Openssl Digitally Sign File
NAMEopenssl-dgst - perform digest operations SYNOPSISopenssl dgst - digest -help -c -d -hex -binary -r -out filename -sign filename -keyform arg -passin arg -verify filename -prverify filename -signature filename -sigopt nm: v -hmac key -fips-fingerprint -rand file. -engine id -engineimpl file.openssl digest.
Openssl Sign String
DESCRIPTIONThe digest functions output the message digest of a supplied file or files in hexadecimal. The digest functions also generate and verify digital signatures using message digests.The generic name, dgst, may be used with an option specifying the algorithm to be used. The default digest is sha256. A supported digest name may also be used as the command name.
To see the list of supported algorithms, use the list -digest-commands command. OPTIONS -helpPrint out a usage message.
The digest functions output the message digest of a supplied file or files in hexadecimal. Digitally sign the digest using the private key in 'filename'.
digestSpecifies name of a supported digest to be used. To see the list of supported digests, use the command list -digest-commands.cPrint out the digest in two digit groups separated by colons, only relevant if hex format output is used.dPrint out BIO debugging information.hexDigest is to be output as a hex dump. This is the default case for a 'normal' digest as opposed to a digital signature. See NOTES below for digital signatures using -hex.binaryOutput the digest or signature in binary form.rOutput the digest in the 'coreutils' format, including newlines. Used by programs like sha1sum.out filenameFilename to output to, or standard output by default.sign filenameDigitally sign the digest using the private key in 'filename'. Note this option does not support Ed25519 or Ed448 private keys.
Openssl Digitally Sign File Online
Use the pkeyutl command instead for this.keyform argSpecifies the key format to sign digest with. The DER, PEM, P12, and ENGINE formats are supported.sigopt nm: vPass options to the signature algorithm during sign or verify operations.
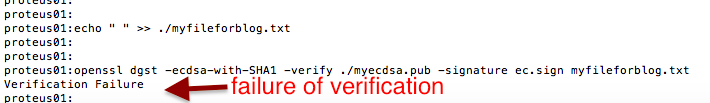
Names and values of these options are algorithm-specific.passin argThe private key password source. For more information about the format of arg see.verify filenameVerify the signature using the public key in 'filename'. The output is either 'Verification OK' or 'Verification Failure'.prverify filenameVerify the signature using the private key in 'filename'.signature filenameThe actual signature to verify.hmac keyCreate a hashed MAC using 'key'.The command should be preferred to using this command line option.mac algCreate MAC (keyed Message Authentication Code).
The most popular MAC algorithm is HMAC (hash-based MAC), but there are other MAC algorithms which are not based on hash, for instance gost-mac algorithm, supported by ccgost engine. MAC keys and other options should be set via -macopt parameter.The command should be preferred to using this command line option.macopt nm: vPasses options to MAC algorithm, specified by -mac key. Following options are supported by both by HMAC and gost-mac: key:stringSpecifies MAC key as alphanumeric string (use if key contain printable characters only).
String length must conform to any restrictions of the MAC algorithm for example exactly 32 chars for gost-mac. Hexkey:stringSpecifies MAC key in hexadecimal form (two hex digits per byte).
Key length must conform to any restrictions of the MAC algorithm for example exactly 32 chars for gost-mac.The command should be preferred to using this command line option.rand file.A file or files containing random data used to seed the random number generator. Multiple files can be specified separated by an OS-dependent character. The separator is; for MS-Windows, for OpenVMS, and: for all others.writerand fileWrites random data to the specified file upon exit. This can be used with a subsequent -rand flag.fips-fingerprintCompute HMAC using a specific key for certain OpenSSL-FIPS operations.engine idUse engine id for operations (including private key storage). This engine is not used as source for digest algorithms, unless it is also specified in the configuration file or -engineimpl is also specified.engineimplWhen used with the -engine option, it specifies to also use engine id for digest operations. File.File or files to digest.
If no files are specified then standard input is used. EXAMPLESTo create a hex-encoded message digest of a file: openssl dgst -md5 -hex file.txtTo sign a file using SHA-256 with binary file output: openssl dgst -sha256 -sign privatekey.pem -out signature.sign file.txtTo verify a signature: openssl dgst -sha256 -verify publickey.pem -signature signature.sign file.txt NOTESThe digest mechanisms that are available will depend on the options used when building OpenSSL. The list digest-commands command can be used to list them.New or agile applications should use probably use SHA-256. Other digests, particularly SHA-1 and MD5, are still widely used for interoperating with existing formats and protocols.When signing a file, dgst will automatically determine the algorithm (RSA, ECC, etc) to use for signing based on the private key's ASN.1 info.
When verifying signatures, it only handles the RSA, DSA, or ECDSA signature itself, not the related data to identify the signer and algorithm used in formats such as x.509, CMS, and S/MIME.A source of random numbers is required for certain signing algorithms, in particular ECDSA and DSA.The signing and verify options should only be used if a single file is being signed or verified.Hex signatures cannot be verified using openssl. Instead, use 'xxd -r' or similar program to transform the hex signature into a binary signature prior to verification.The command is preferred over the -hmac, -mac and -macopt command line options. SEE ALSOHISTORYThe default digest was changed from MD5 to SHA256 in OpenSSL 1.1.0. The FIPS-related options were removed in OpenSSL 1.1.0.
COPYRIGHTCopyright 2000-2019 The OpenSSL Project Authors. All Rights Reserved.Licensed under the Apache License 2.0 (the 'License'). You may not use this file except in compliance with the License. You can obtain a copy in the file LICENSE in the source distribution or at.You are here::::::.This manpage.Please report problems with this website to webmaster at openssl.org.Copyright © 1999-2018, OpenSSL Software Foundation.
Sometimes you might want to deploy a file, like a tarball, with an embeddedpublic/private key signature so that a recipient can validate that the file camefrom the source they think it came from. Easeus data recovery serial key free. This technique is often used fordeploying software updates.Generally, a public/private key signature is distributed separate from the fileof interest. For example, most Linux distributions will provide a signaturedigest file or hash checksum value for people who download the distributioninstaller to check the installer against. This works fine but it requires 2files, it could be more convenient to have both the file itself and thesignature concatenated together in such a way that it’s easy to work with.A way that I’ve found to accomplish this using OpenSSL (so as to avoid usingGnuPG) follows these exact steps:First, create an 2048 bit RSA private key using openssl ( KEEP THIS PRIVATE KEYSECRET!).